- download pcap file
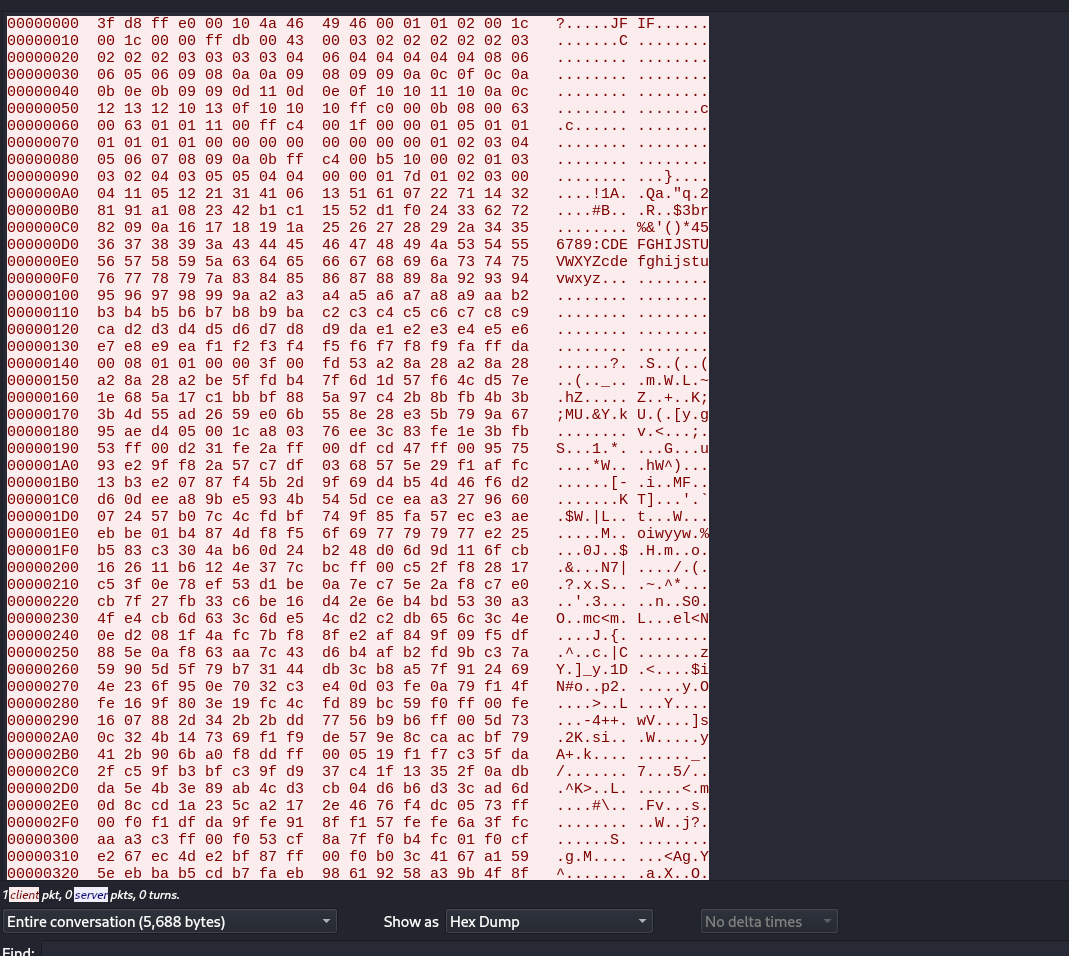
- follow tcp stream
- contain jpg file but it is corrupt
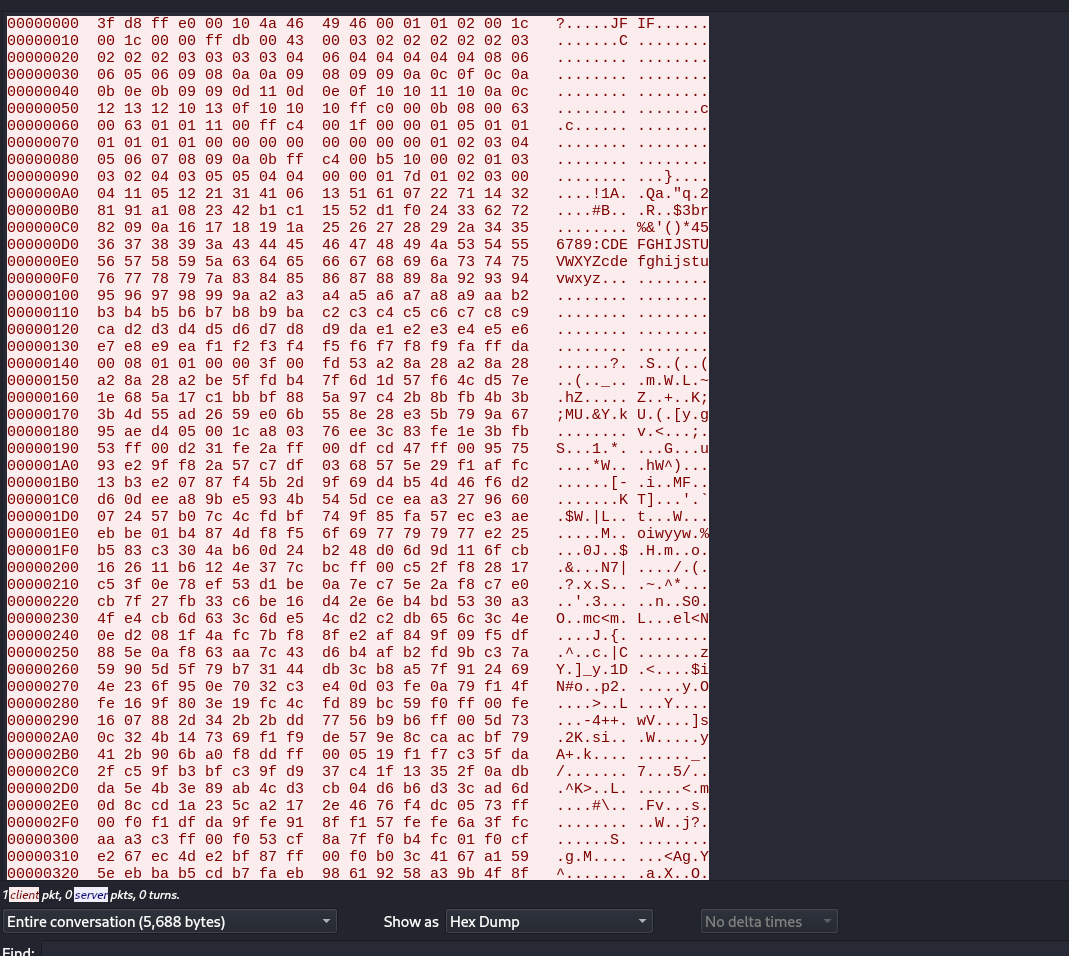
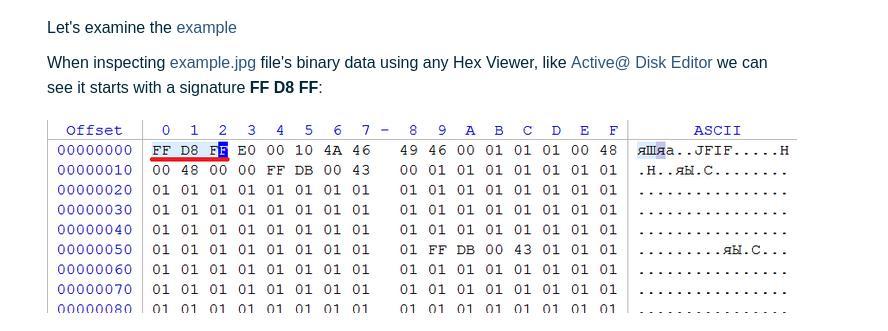
using any hex editor change 3f to ff as jpeg JFIF header
save this dump in dump.txt
| |
- gives this qr

- apporvctf{this_aint_it_brother}
- dead end
- we are onto it
| |
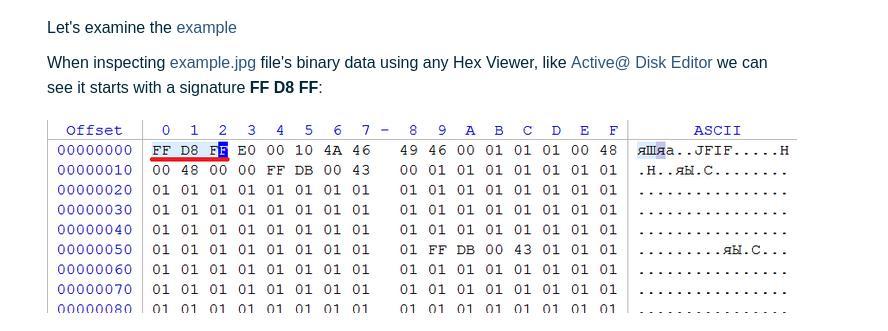
using any hex editor change 3f to ff as jpeg JFIF header
save this dump in dump.txt
| |

| |