network enumaration
- nmap scan
| |
- result
| |
- check webpage
- use gobuster to enumrate directory
| |
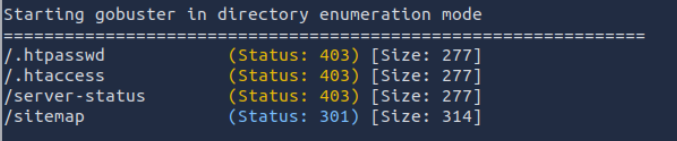
- checked site can’t find form or any parameter in url
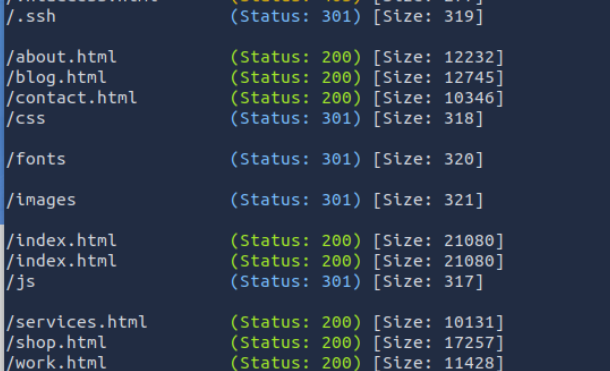
- maybe enumarate more
| |
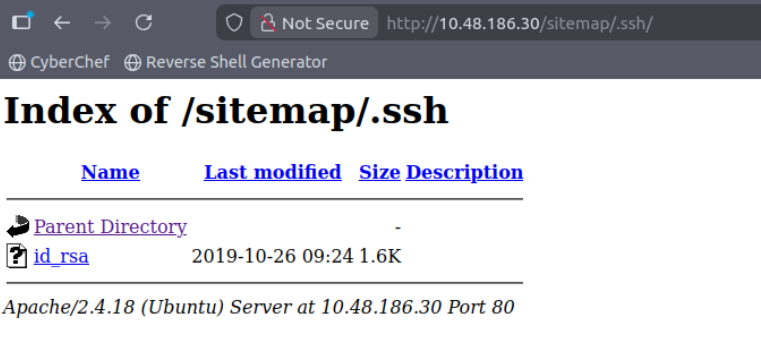
i have private key
but i still don’t have username for ssh
user enumaration
on about page i found few username
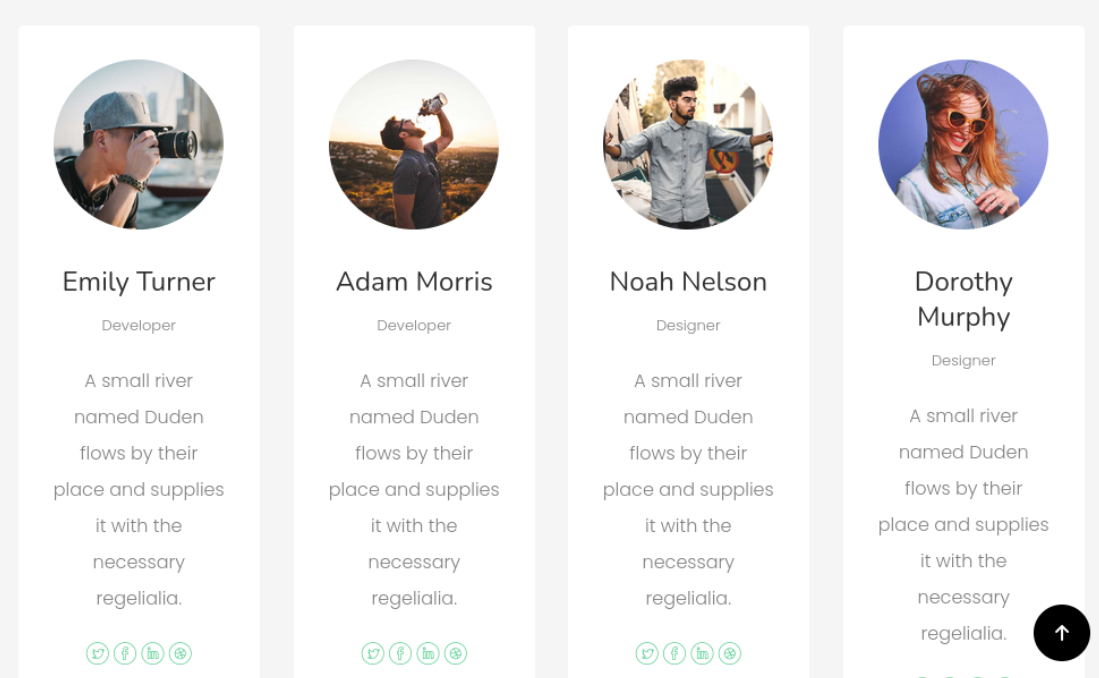
i tried all did not work
check source code
on webpage i found this comment
| |
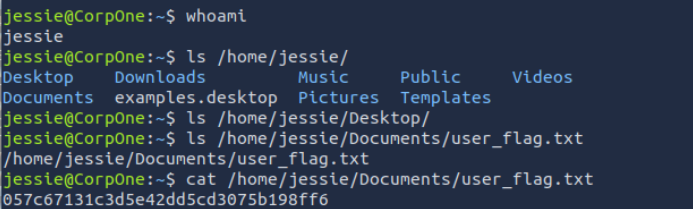
- use this credentials
| |
privilage escalation
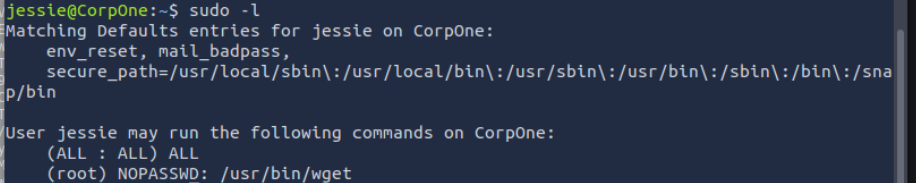
- so i tried file read GTFO
| |
- & we have root flag